57 herramientas de análisis y seguridad web
En Techbeacon crearon una lista de 57 herramientas de código abierto dedicadas a análisis de aplicaciones web.
 Algunos de estos proyectos son muy activos y se actualizan con frecuencia con nuevas capacidades, algunas "gratis" o "ediciones de la comunidad" y otras tienen versiones comerciales más completas.
Algunos de estos proyectos son muy activos y se actualizan con frecuencia con nuevas capacidades, algunas "gratis" o "ediciones de la comunidad" y otras tienen versiones comerciales más completas.
SANS también ha publicado el SANS 2016 State of Application Security
También han publicado un informe SANS 2016 State of Application Security
- Andiparos A fork of the famous Paros Proxy, an open source web application security assessment tool that gives penetration testers the ability to spider websites, analyze content, intercept, and modify requests https://code.google.com/archive/p/andiparos
- Arachni Penetration testing environment; Ruby framework focus
- BackTrack Called a Linux-based penetration testing arsenal, this distribution is configured with hundreds of security testing tools and scripts
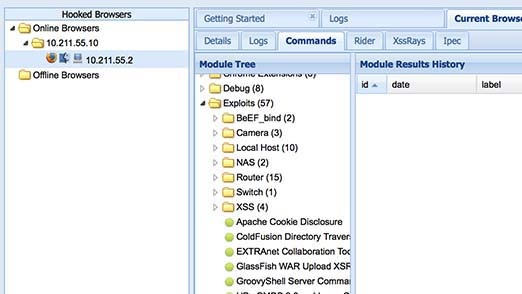
- BeEF Penetration testing for Open Source
- Caja Compiler for making third-party HTML, CSS and JavaScript safe to embed in a website. It uses an object-capability security model to allow for a wide range of flexible security policies http://developers.google.com/caja
- ClamAV Open source antivirus engine for detecting trojans, viruses, malware & other malicious threats
- DOM Snitch Experimental Chrome extension that enables developers and testers to identify insecure practices commonly found in client-side code. Developers and testers can observe DOM modifications as they happen inside the browser without the need to step through JavaScript code with a debugger or pause the execution of their application
- Ettercap Called "a comprehensive suite for man in the middle attacks... features sniffing of live connections, content filtering on the fly and many other interesting tricks." http://ettercap.github.io/ettercap
- GoLismero Free software framework for security testing
- Google hacking database (GHDB) Described by SecTools.org as "a gold mine for security researchers and penetration testers," this site is part of The Exploit Database, "a non-profit project that is provided as a public service by Offensive Security."
- Google application security tools Google states that these tools "address a gap present in other open-source tools. These tools may require some minor tweaking or compilation to work on your systems." Some are included separately in this list
- Grabber Web application scanner which can detect many security vulnerabilities in web applications. An open source web application penetration testing tools
- Grendel Scan web application security tool for finding security vulnerabilities; features are also available for manual penetration testing
- Gruyere Called “a small, cheesy web application”; allows users to publish snippets of text and store assorted files. Caveat: Gruyere has multiple security bugs ranging from cross-site scripting and cross-site request forgery, to information disclosure, denial of service, and remote code execution
- Kali Linux penetration testing
- Keyczar Open source cryptographic toolkit designed to make it easier and safer for developers to use cryptography in their applications. It supports authentication and encryption with both symmetric and asymmetric keys; designed to be an open, extensible and cross-platform compatible
- Kismet Wireless network detector, sniffer, and intrusion detection system. Kismet works predominately with Wi-Fi (IEEE 802.11) networks, but can be expanded via plug-ins to handle other network types
- Malwarebytes Endpoint security malware scanner for Windows
- Metasploit Metasploit by Rapid7 Penetration Testing Open Source
- ModSecurity WAF open source
- Nagios Monitors the entire IT infrastructure to ensure systems, applications, services, and business processes are functioning properly
- Native Client (NaCl) A technology for running native compiled code in the browser. NaCl aims at maintaining operating system portability and safety that people expect from web applications http://developer.chrome.com/native-client
- Nikto2 Web server testing tool to find known vulnerable scripts, configuration mistakes and related security problems
- Nmap Penetration testing utility for network discovery and security auditing with NSE scripts that can detect vulnerabilities, misconfiguration and security related information around network services
- NoScript Firefox addon that provides extra protection for Firefox, Seamonkey and other mozilla-based browsers; allows JavaScript, Java, Flash and other plugins to be executed only by trusted web sites of your choice
- OpenSSH Secures traffic between two points by tunnelling insecure protocols through an SSH tunnel http://www.openssh.com
- OpenVAS Open source vulnerability scanning suite
- OSSEC Host based intrusion detection system or HIDS
- OWASP A large class of open source sec testing tools is available at owasp.org
- Packet Storm Wide variety of scanner tools for vulnerability and penetration available http://packetstormsecurity.org/files/tags/scanner
- Paros Proxy Testing tool for your security and vulnerability testing. Used to spider/crawl entire sites, then execute canned vulnerability scanner tests
- Powerfuzzer HTTP protocol based application fuzzer based on many other Open Source fuzzers http://www.powerfuzzer.com
- Ratproxy Designed to overcome the problems users usually face while using other proxy tools for security audits; capable of distinguishing between CSS stylesheets and JavaScript codes https://code.google.com/archive/p/ratproxy
- Secunia PSI A free computer security solution that identifies vulnerabilities in applications on private PCs http://learn.flexerasoftware.com/SVM-EVAL-Personal-Software-Inspector
- Security Onion Linux distribution for intrusion detection, network security monitoring, and log management http://blog.securityonion.net
- Skipfish Active web application security reconnaissance tool. It prepares an interactive sitemap for a site by carrying out a recursive crawl and dictionary tools. Written in C with a custom HTTP stack, it is high performance, easy to use and reliable
- Snort Open-source, free and lightweight network intrusion detection system (NIDS) for UNIX derivatives and Windows
- SonarQube SonarQube™ software (previously known as "Sonar") is an open platform to manage code quality. As such, it covers the 7 axes of code quality
- SQLMap Penetration testing tool, automates the process of finding and exploiting SQL injection vulnerability in a website’s database
- Tcpdump Called "a powerful command-line packet analyzer" on its website, this tool is still used by many as an alternative to the more resource-intensive Wireshark
- Vega Web vulnerability scanner and testing platform; SQL injection, cross-site scripting, etc. https://subgraph.com/vega
- W3AF SQL injection, cross-site scripting detection tool
- Wapiti Web vulnerability scanner which lets you audit the security of your web applications. It performs black-box testing by scanning web pages and injecting data http://wapiti.sourceforge.net
- Watcher A Fiddler addon to assist penetration testers in passively finding Web app vulnerabilities http://websecuritytool.codeplex.com
- WATOBO Perform efficient (semi-automated) web application security audits http://watobo.sourceforge.net/index.html
- WebScarab Java-based security framework for analyzing web applications using HTTP or HTTPS protocol. Written in Java, portable to many platforms; offers several modes of operation, implemented by a number of plugins. In its most common usage, WebScarab operates as an intercepting proxy
- Websecurify GNUCITIZEN (see the Commercial vendor list)
- Wfuzz A freely available open source tool for web application penetration testing. It can be used to brute force GET and POST parameters for testing against various kinds of injections like SQL, XSS, LDAP, and many others
- SensePost Vulnerability tools for devices, networks, and apps. Tools include autoDANE, reGeorg, Jack, and the SensePost Maltego Toolset
- Wireshark Wireshark Penetration Testing and Packet-level Monitoring Open Source; view traffic in as much detail as you want; follow network streams and find problems
- Zed Attack Proxy Also known as Zap. Open source, intercepting proxy which is fork and update of the badly out of date Paros Proxy. Fairly powerful for manual testing, and contains some automated testing features. https://www.owasp.org
http://www.arachni-scanner.com
http://www.backtrack-linux.org
http://beefproject.com
http://clamav.net
https://code.google.com/archive/p/domsnitch
http://www.golismero.com
https://www.exploit-db.com/google-hacking-database
https://www.google.com/about/appsecurity/tools
http://rgaucher.info/beta/grabber
https://sourceforge.net/projects/grendel
http://google-gruyere.appspot.com
http://kali.org
https://github.com/google/keyczar
http://kismetwireless.org
http://malwarebytes.org
http://metasploit.com
http://modsecurity.org
http://nagios.org
http://cirt.net/nikto2
http://nmap.org
http://noscript.net
http://openvas.org
http://ossec.github.io
https://www.owasp.org/index.php/Appendix_A:_Testing_Tools
http://www.testingsecurity.com/paros_proxy
https://code.google.com/archive/p/skipfish
http://snort.org
https://github.com/SonarSource/sonarqube
http://sqlmap.org
http://tcpdump.org
http://w3af.org
http://www.owasp.org/index.php/Category:OWASP_WebScarab_Project
http://code.google.com/p/wfuzz
http://sensepost.com
http://wireshark.org
SANS también ha publicado el SANS 2016 State of Application Security
También han publicado un informe SANS 2016 State of Application Security



Que buen resumen de herramientas y un buen inicio para iniciar en la automatización de algunas pruebas.
ResponderBorrarsaludos.
Excelente resumen
ResponderBorrar